The EU Cyber Resilience Act: Guide
trait de séparation
8 min de lecture • April 2026
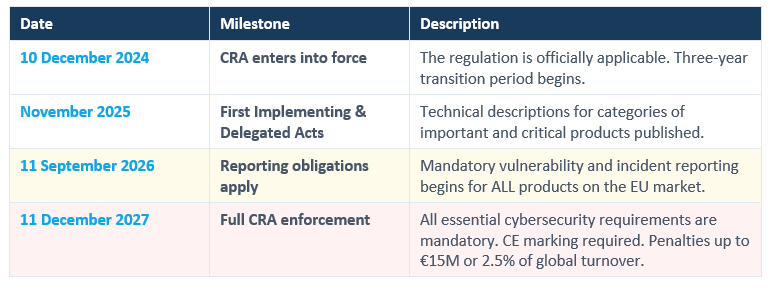
Regulation (EU) 2024/2847, often referred to as the Cyber Resilience Act (CRA), came into force on 10 December 2024. This text represents the most ambitious legislation on product cybersecurity, whether hardware or software, within the European Union. The first implementation deadline is set for September 2026, leaving little time to prepare.
For over 30 years, ISIT has been supporting engineering teams in sectors such as aerospace, automotive, healthcare and industry, helping them to design and certify embedded systems that are both safe and secure. The CRA has a direct impact on the products our clients develop every day.
This article summarises the requirements of the regulation to provide you with a clear and practical overview.

What Is the Cyber Resilience Act?
The Cyber Resilience Act establishes mandatory, EU-wide cybersecurity requirements for all products with digital elements. It addresses a gap in previous legislation (NIS2, EU Cybersecurity Act).
CRA compliance will be part of CE marking. National market surveillance authorities will enforce the rules, with support from ENISA.
CRA compliance will be part of CE marking. National market surveillance authorities will enforce the rules, with support from ENISA.
Source : Règlement (UE) 2024/2847, art. 2(1) et art. 3(1) ; Annexe Ares, sections 2.1–2.4.
3 Pillars of the Cyber Relience Act
Secure by Design
Products must be designed, developed, and produced to ensure an appropriate level of cybersecurity from the first architecture decisions.
Secure Through Lifecycle
Manufacturers must handle vulnerabilities continuously after the product is sold, provide free security updates, and maintain monitoring (min. 5 years).
Transparency for Users
Users must be given clear information to consider cybersecurity when selecting products: documentation, support period end date, SBOM data, if necessary.
Source : Règlement (UE) 2024/2847, Annexe I.
Requirements of the Cyber Resilience Act
Essential Obligations for Manufacturers
Products must ship with no known exploitable vulnerabilities, a secure default configuration, data protection and proper access controls. The Commission’s guidance emphasises that cost considerations are irrelevant.
Source : Règlement (UE) 2024/2847, Annexe I ; Annexe Ares, sections 5 et 7.
Reporting Obligations: First Deadline September 2026
Article 14 introduces mandatory reporting of actively exploited vulnerabilities and severe security incidents. This applies from 11 September 2026 and covers ALL products already on the EU market.
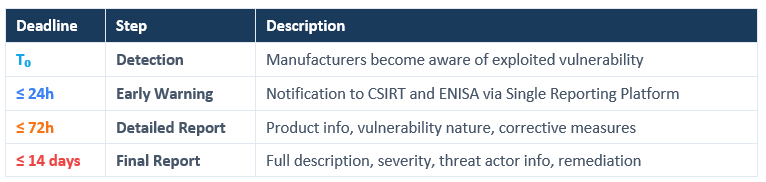
For severe incidents, the final report deadline extends to one month. The Commission’s guidance clarifies that manufacturers are deemed “aware” once they have a reasonable degree of certainty.
Source : Règlement (UE) 2024/2847, art. 14 ; Annexe Ares, section 9.1.
Cyber Relience Act Implementation Timeline
Product Classification: Default, Important & Critical
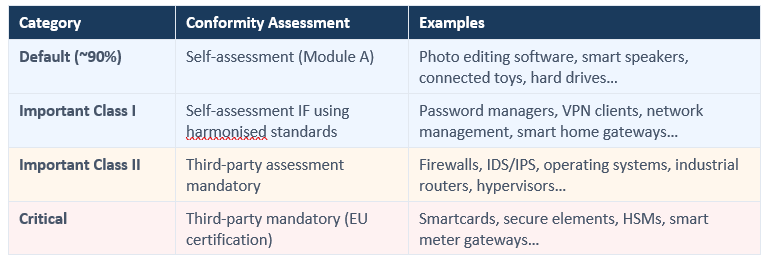
The Commission’s guidance introduces the concept of “core functionality”. A product integrating a component from a higher category does not automatically inherit that category.
Source : Annexe Ares, sections 6.1–6.2 ; Règlement (UE) 2024/2847, art. 7–8.
Where do certain product threats or weaknesses come from?
● Third-party components — Modern applications contain 70–90% third-party code (open-source libraries, SDKs, middleware)
● Legacy code debt — Outdated codebases with unpatched vulnerabilities accumulated over years
● AI-generated code — Vulnerable patterns from training data, code without clear provenance
● Weak encryption — Outdated algorithms or poor implementation of cryptographic protocols
● Unlicensed OSS snippets — Open-source code used without proper tracking or license compliance
● Insecure programming languages — Memory safety issues in C/C++ without proper verification
The CRA does not allow manufacturers to transfer cybersecurity risk to users or third parties.
● Legacy code debt — Outdated codebases with unpatched vulnerabilities accumulated over years
● AI-generated code — Vulnerable patterns from training data, code without clear provenance
● Weak encryption — Outdated algorithms or poor implementation of cryptographic protocols
● Unlicensed OSS snippets — Open-source code used without proper tracking or license compliance
● Insecure programming languages — Memory safety issues in C/C++ without proper verification
The CRA does not allow manufacturers to transfer cybersecurity risk to users or third parties.
Source : Annexe Ares, section 7.1.
Software Composition Analysis: One of the Keys to Transparency
The Cyber Resilience Act requires manufacturers to maintain a Software Bill of Materials (SBOM). While formally enforceable in December 2027, the September 2026 reporting deadline means you cannot report what you don’t know. Without an accurate component inventory, detecting vulnerabilities is difficult.
Free and Open-Source Software Under the CRA
Free software that is not monetised and is not marketed commercially is not subject to the CRA. The CRA introduces the concept of ‘open-source software stewards’, who are subject to a simplified regime (Article 24). For manufacturers who incorporate open-source components into commercial products, the full obligations apply.
Source : Annexe Ares, section 3 ; Règlement (UE) 2024/2847, considérants 17–22.
The Cyber Resilience Act: How ISIT helps you achieve compliance
Solution
Outil
Description
Supply chain & SBOM
SCANOSS : CBOM, SBOM, AI BOM
Generate comprehensive Software Bills of Materials for third-party component visibility. Essential for CRA transparency and reporting requirements.
VHDL Code Quality
Linty
Identify and fix weaknesses in VHDL code for FPGA and ASIC designs. Meet cybersecurity expectations from the design phase.
Memory Safety Verification
Formal proof of absence of memory safety issues in C/C++ software — addressing one of the most critical vulnerability categories for embedded software.
Training
Helps department heads, quality managers and product managers to assess the impact of the CRA on CE marking and the entire product lifecycle.
Our consultants also support pre-audits, risk assessments, and the development of compliant processes aligned with IEC 62443, ISO 21434, and the CRA.
Start your Cyber Resilienc Act compliance journey today
Sources & Références
1. Regulation (EU) 2024/2847 — Cyber Resilience Act, Official Journal of the EU, 20.11.2024. http://data.europa.eu/eli/reg/2024/2847/oj
2. European Commission Draft Guidance — CRA application (Ares annex), published for feedback 03.03.2026. https://digital-strategy.ec.europa.eu/en/policies/cyber-resilience-act
3. EC CRA Summary & FAQs. https://digital-strategy.ec.europa.eu/en/policies/cra-summary
4. Commission Implementing Regulation (EU) 2025/2392 — Technical descriptions for important and critical product categories.