Taint Analysis, Functional Safety, Cybersecurity, and you
trait de séparation
Webinar on-demand • March 2026
Connectivity has transformed the mindset of embedded system developers by expanding the scope of what their creations can achieve. It has shifted the focus from standalone devices to interconnected systems, leading to considerations of interoperability, data utilization, remote capabilities, user experience and, particularly, security.
Taint analysis plays a crucial role in enhancing the security posture of embedded software systems. It helps developers and security professionals to identify and address potential vulnerabilities related to the handling of sensitive or untrusted data. As an integral part of secure coding practice, it is an important component in the development of resilient and robust embedded software applications.
This webinar will discuss taint analysis in the context of a structured software development environment, relating it to established secure- and safety- critical applications alike. The discussion will explain how both of those considerations can be addressed concurrently in a development lifecycle. The presentation will conclude by discussing appropriate tooling designed to achieve those aims.
Definition : Taint Analysis
Taint analysis is a technique that tracks the propagation of potentially unreliable or dangerous data (called tainted data) through a program.
Objective: To identify whether external data (user input, files, network, environment variables, etc.) reaches sensitive areas (sinks) such as:
- system command execution,
- SQL queries,
- memory manipulation,
- file writing,
- privileged calls.
It is used in particular to detect vulnerabilities such as:
- SQL injections,
- command injections,
- XSS,
- buffer overflows.
The steps involved in Taint Analysis
1. Definition of sources (sources of taint)
These are the entry points where unreliable data can arrive:
2. Data labeling
As soon as data comes from an unreliable source, it is marked as tainted.
The analysis engine keeps this label in memory throughout the program.
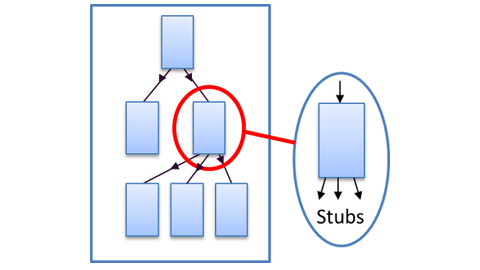
3. Taint propagation
Contamination spreads through program operations:
a = user_input → a is tainted
b = a + “test” → b also becomes tainted
c = sanitize(b) → depending on the function, c may be cleaned or remain tainted
Propagation can be:
4. Definition of sinks (sensitive points)
A sink represents an action that is considered dangerous if it receives unreliable data:
5. Rule verification / Sanitation
Before tainted data reaches a sink, the analysis checks:
6. Vulnerability detection and reporting
If contaminated data reaches a sink without having been sanitized:
These are the entry points where unreliable data can arrive:
- user input (stdin, form fields, API),
- network data,
- external files,
- environment variables.
2. Data labeling
As soon as data comes from an unreliable source, it is marked as tainted.
The analysis engine keeps this label in memory throughout the program.
3. Taint propagation
Contamination spreads through program operations:
a = user_input → a is tainted
b = a + “test” → b also becomes tainted
c = sanitize(b) → depending on the function, c may be cleaned or remain tainted
Propagation can be:
- explicit (assignments, concatenations, calculations),
- implicit (flow control, conditions).
4. Definition of sinks (sensitive points)
A sink represents an action that is considered dangerous if it receives unreliable data:
- exec() / system() / shell,
- SQL queries,
- Writing to a sensitive file,
- Critical system calls.
5. Rule verification / Sanitation
Before tainted data reaches a sink, the analysis checks:
- whether it passes through a sanitizer function,
- whether the function is reliable,
- whether the transformation neutralizes the threat.
6. Vulnerability detection and reporting
If contaminated data reaches a sink without having been sanitized:
- an alert is raised,
- the tool reports the dangerous execution path,
- the developer can correct it.